
Note: This is a guest post written by Marcus Jensen
As of the middle of July 2016, there have been more than 500 reported security breaches with more than 13 million records exposed (the number doesn’t include breaches that haven’t been reported). Targets that were affected by the rising “trend” of cyber security breaches were telecom providers, health-care organizations and federal agencies.
We have witnessed big data breaches in 2015 that showed us the real importance of cyber-protecting important and sensitive data. How cyber attackers keep infiltrating networks to steal confidential information has made data breaches become a status quo. The most impactful breaches of this year so far are presented in the list below. Let’s take a look.
FBI, Department of Homeland Security
Hackers threatened to, and eventually managed to find an infiltration path and dump the records of almost 30 thousand DHS and FBI workers. Personal information, including names, job titles, phone numbers and email addresses were included in these records.
The perpetrator claimed that he had access to even more files (total of 200GB), and have gained access to the FBI’s Intranet by compromising US Department of Justice email account, when he allegedly downloaded all the information.
21st Century Oncology
According to the statement on their website, this company which offers cancer caring services has had its personal information stolen during a security breach in October 2015. The hack was discovered a month later, but the company was discouraged by the FBI to make a public announcement until March 2016.
Hackers gained access to patients’ names, insurance information, Social Security numbers, diagnosis information and doctors’ names. There is no evidence, however, that the sensitive data has been used in any way.
TeamViewer
TeamViewer is a remote and online meeting software used around the world (it has one billion installations, according to the company’s claims). Nevertheless, its customers have been experiencing cyber invasions, while the company is denying anything related to these claims.
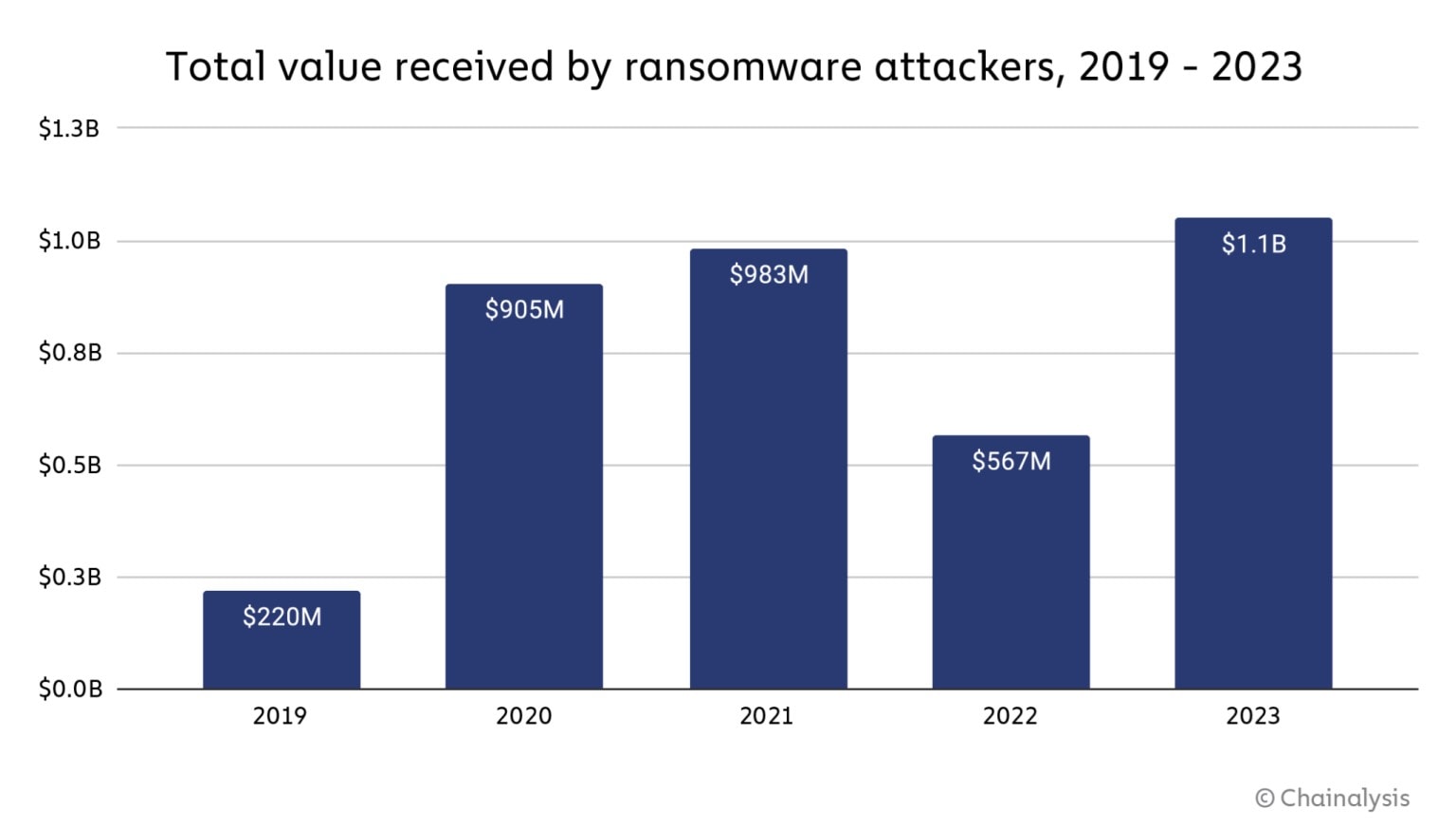
Cyber-attacks may have begun in May, and include accessing and pilfering Amazon, PayPal and bank accounts using stolen passwords, as well as installing ransomware.
With the access gained through TeamViewer, attackers can take remote control of the users’ computers in off hours. TeamViewer stated on May 23rd 2016 that the causes of reported issues were not due to potential security breaches, but to careless use. Only a week later the company experienced a DDoS (Distributed Denial of Service) attack, which they reported, and a DoS (denial-of-service) attack aimed at their DNS-Server Infrastructure, saying there is no evidence that these issues are related to the past hack claims.
Hacking TeamViewer can be a very profitable criminal act, because connecting global clients is the company’s primary service.

A data breach, which occurred in 2012, came back in mid-May to haunt LinkedIn. Namely, personal information of 117 million users was stolen and turned up for sale online. According to remote server monitoring and automation experts Secure Link, it is possible that this breach is related to the TeamViewer breach, with TeamViewer users still reporting hijacked computers, in spite of strengthened security.
Affected LinkedIn users were told to reset their passwords at the time the breach occurred, and that information became publicly available this May. Passwords of all LinkedIn accounts created prior to the breach have been invalidated by the company.
LinkedIn is still working with law enforcement officials to find out who conducted the attack, but it is still not clear who stole the information and published it.
Dropbox
Another past breach came back to haunt, affecting 68 million Dropbox users. The initial data breach occurred in 2012, but the username and password theft was not revealed until the end of August 2016.
At this time, it doesn’t appear that the accounts have been accessed illegally. Dropbox prompted their users who have not reset their passwords in the last four years to do so.
Note: This guest post was written by Marcus Jensen from technivorz.com You can follow him on Twitter @marcusTJensen





Comments are closed.