Note: This post was written by a guest contributor
It’s no secret that the internet can be a very powerful tool when it comes to business. With all the scope of social networking, brand awareness and the comparative low costs, it’s no wonder than not only do businesses fully utilise the internet during the working day, but set up online shops to complement their brick and mortar establishments.
That said, there are some nasty things out there in the cyber world – and not being adequately protected from them could spell disaster for any company – especially a growing one. Certain information and data needs to be kept safe, and any potential security threats need to be destroyed before they have the chance to cause any damage.
Even if you are a private user, you could do much worse than taking these online security measures into account.
The risks
At risk from security breaches are any of your IT-based services and equipment. Any data which is stored on IT equipment can be compromised, and it’s of utmost importance to protect it. Threats can take the form of viruses, theft of equipment and remote attacks on an internal network.
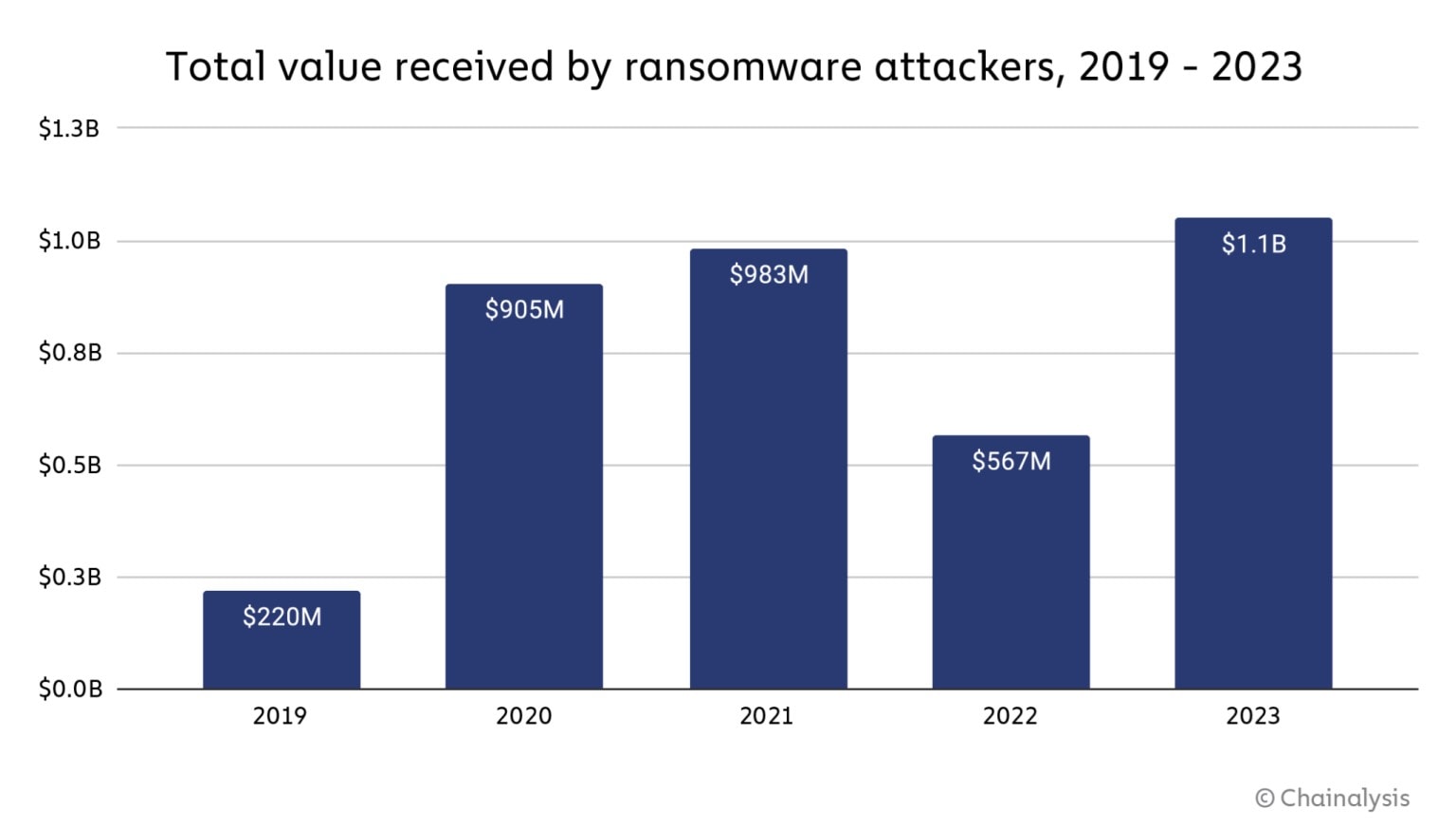
The financial implications of losing valuable data are insurmountable. It’s well worth investing on the right protection.
Prevention
Viruses can be picked up from websites, from the opening of emails or from the running of malicious .EXE files. Trojans, worms and spyware can greatly inhibit the progress of work, and can bring the security level of important documents under question.
As standard, you should issue all IT equipment with anti-virus software and malware protection. It’s also worth restricting access to certain untrustworthy websites, and implementing blocks on certain webpages.
Additional backup and malware protection can be attained with programs such as malwarebytes, which can detect malware before it hits. It can also detect malware previously installed on a computer or laptop and remove it effectively.
Pre-emptive strikes
A recently released security management system, log analysis can be a well-worthy addition to IT security within a small business. Providing the means of which to allow businesses to find potential security threats without needing to go through millions of log files manually, RandomStorm’s StormAgent cuts the fuss from keeping on track of security threats.
Able to identify any changes within the network infrastructure, rules-based custom reports can show administrators any suspicious activity with very little effort. Any signs of hacking can be seen and assessed quickly.
Keeping up to date
Viruses and hacking programs are constantly being created and improved, so it’s in the interests of every business to keep on top of it. Having a regularly-updated anti-virus software program is paramount, and tutoring staff on the ins and outs of internet security is well worth the time invested.
And, as you’ll have read in Craving Tech’s previous post concerning the hacking of Facebook’s network which revealed the contact info of 6 million users, it’s not just the internal workings of your company that needs to be kept a close eye on. Fox news recently covered secure alternatives to Facebook, Instagram and Twitter.